Short Tutorial: Reverse Engineering Tool radare2

radare2 is a reverse engineering tool/framework that is extremely useful for disassembling, debugging, patching, and analyzing binaries. This tool is pre-installed on the popular Kali Linux operating system. radare2 is based on a command-line interface tool. This blog covers installation/ uninstallation and utilities available in radare2 tool.
Installation
You can install it by using the below set of commands:
git clone https://github.com/radareorg/radare2 cd radare2 sudo sys/install.sh
Uninstallation
make uninstall make purge
Utilities available with radare2
| rax2 | helps in base conversions |
| rabin2 | extract information from executable binaries |
| radiff2 | display differences |
| radare2 | main tool in the framework |
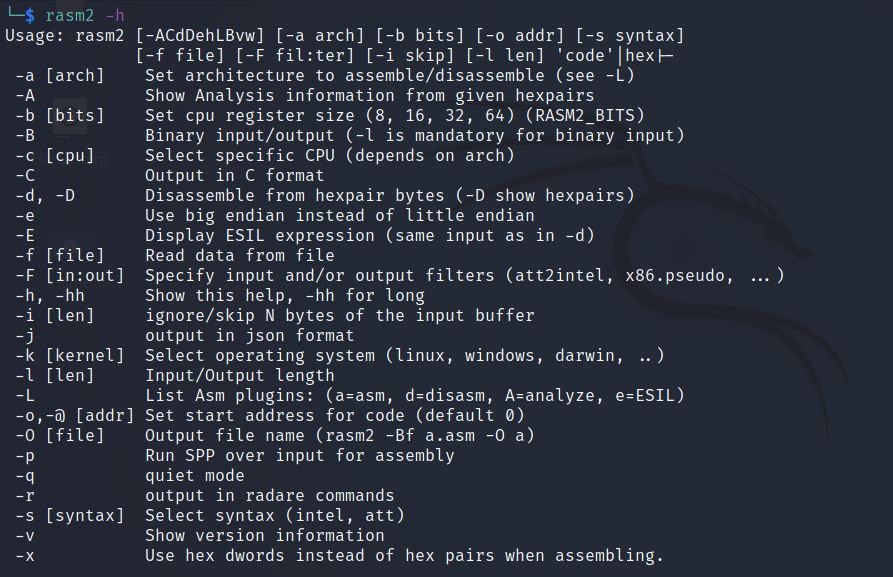
| rasm2 | support multiple architectures including Intel x86, x86-64 for assembling and disassembling |
| rahash2 | supports multiple cryptographic algorithms to check the integrity of files |
| rafind2 | help in finding byte patterns in files |
| ragg2 | compile high-level program into binaries (x86, x86-64, ARM) |
| rarun2 | Useful for Solving crackmes, Fuzzing and Test suites |
Available options in rax2

Available options in rabin2
rabin2 -I <classes.dex>

Available options in radiff2

Available options in radare2

Available options in rasm2
Available options in rahash2

Available options in rafind2

Available options in ragg2

Available options in rarun2

r2frida
It is a project that allows the connection of radare2 with the popular tool Frida. This project works well both for Android and iOS environments.
Subscribe us to receive more such articles updates in your email.
If you have any questions, feel free to ask in the comments section below. Nothing gives me greater joy than helping my readers!
Disclaimer: This tutorial is for educational purpose only. Individual is solely responsible for any illegal act.








