Top Networking Commands Used by Ethical Hackers

Networking commands play a critical role in identifying critical vulnerabilities. These commands help them to know the IP details, interfaces details, name server details, etc. This blog covers Top Networking Commands Used by Ethical Hackers.
(1) ifconfig
Whenever you want to know the IP address, ifconfig is the command that provides you the IP, interface details, broadcast address, etc.
ifconfig

Usage:

(2) ping
Whenever you know the remote IP of the victim, you want to know whether the remote host is up or not. ping command helps you to identify the state of the remote host.
ping <IP>

Usage:

(3) iwconfig
This command displays wireless interface details. The main difference between ifconfig and iwconfig is ifconfig shows all available interfaces while iwconfig shows only wireless interfaces.
iwconfig

Usage:

(4) netstat
netstat, short for network statistics, is used for troubleshooting network problems. It displays information related to TCO connections, routing tables, etc.
Example
netstat -ano
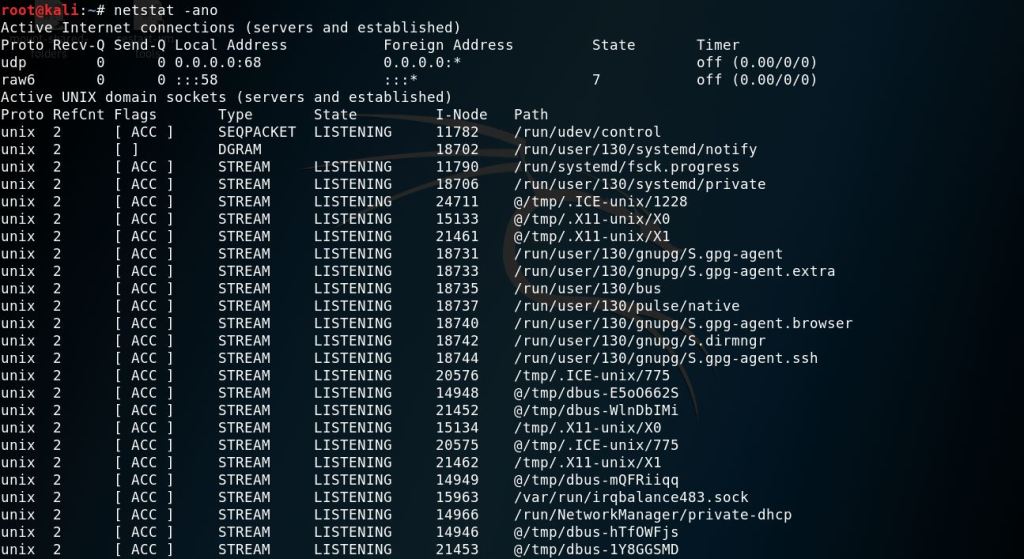
Usage:

(5) arp
arp command displays IP address mapping with mac address. In simple words, this command resolves the IP address of a system to a mac address.
arp -a

Usage:

(6) route
route command displays details of the routing table.
route

Usage:

(7) ip
ip command displays the IP address, subnet mask, broadcast address, etc. You can use this command if ifconfig command is not available.
Examples:
ip a

ip n

ip r

Usage:

(8) ss
ss command is the replacement of netcat. This command shows more information in terms of more socket statistics than netcat.
Example:

Usage:


(9) whois
whois command displays information related to IP address and domain name.
Example:
whois google.com
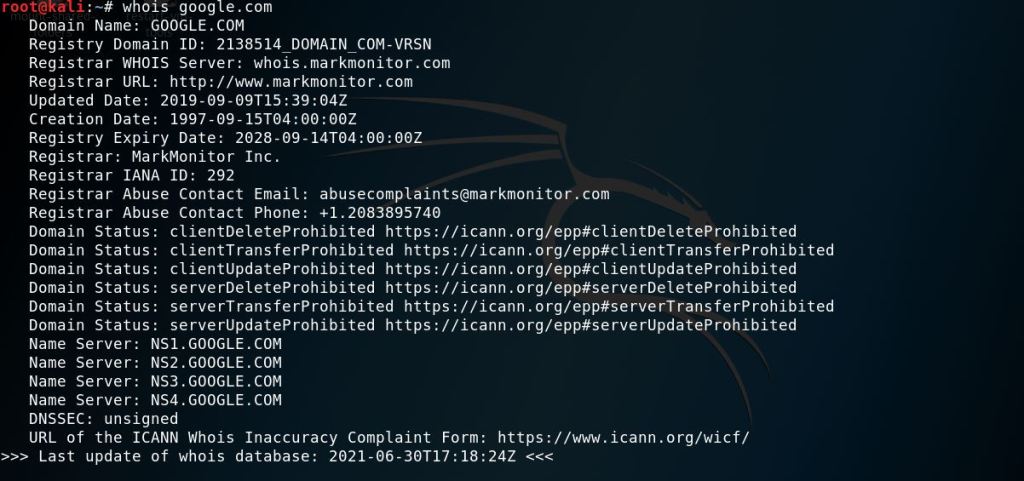
Usage:

(10) hostname
hostname command displays information about the system's hostname.
Usage:

(11) curl or wget
Both commands are used to transfer data via the command line. These two commands are extremely useful in getting files from remote locations.
Usage:


Click Here if you want to know Top 5 Commands to Test DNS Zone Transfer in 2 minutes.
(12) host
host command resolves the URL into an IP address and vice versa. In addition, it helps in getting DNS lookups and troubleshooting DNS-related problems.
host allabouttesting.org
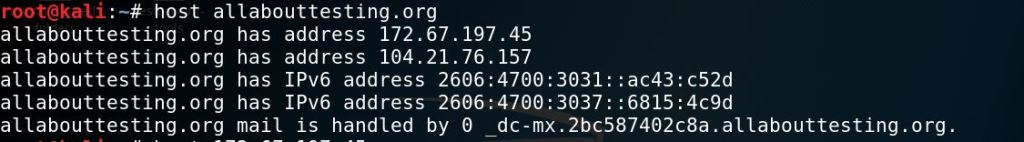
host google.com

host 216.58.196.110

Usage:

Subscribe us to receive more such articles updates in your email.
If you have any questions, feel free to ask in the comments section below. Nothing gives me greater joy than helping my readers!
Disclaimer: This tutorial is for educational purpose only. Individual is solely responsible for any illegal act.








