Quick Tutorial: firmwalker tool for Firmware Analysis

Firmwalker is a tool written in a bash script and it is used for analyzing the file system of extracted or mounted firmware.
Installation
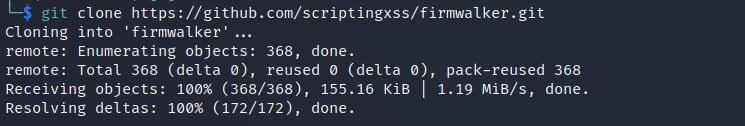
You can install a firmwalker tool by using the one-liner command:
git clone https://github.com/scriptingxss/firmwalker.git
What is the output of firmwalker?
firmwalker provides you quick initial results to initiate security assessment of firmware.
- may give sensitive details by searching keywords such as admin, remote, password etc.
- may give .bin, script, configuration files
- may give IP addresses, email IDs, URLs, etc.
- may give details for etc/shadow, etc/passwd and etc/ssl directories
- may give SSL-related files such as .pem, .crt etc.
How to run firmwalker?
This tool can be run against the filesystem of extracted or mounted firmware. For testing purposes, clone the repository of IoTGoat, an intentionally vulnerable firmware developed by the OWASP community.
git clone https://github.com/OWASP/IoTGoat.git

Now, you can run firmwalker against the filesystem of downloaded IoTGoat
./firmwalker.sh ~/IoTGoat/OpenWrt/openwrt-18.06.2/files

It will search admin, admin pattern, root etc.

Search for the private key

Search for URLs, IP, and email addresses

Conclusion
firmwalker is a great automation tool (or more precisely bash script) to start the assessment of firmware. Although, you need to go through reports and analyze results manually to identify more vulnerabilities.
Subscribe us to receive more such articles updates in your email.
If you have any questions, feel free to ask in the comments section below. Nothing gives me greater joy than helping my readers!
Disclaimer: This tutorial is for educational purpose only. Individual is solely responsible for any illegal act.








