SSH Hardening Tips for Linux Administrators & Security Researchers

SSH, short for Secure SHell, is used to access remote desktops or systems in a secure way. SSH comes with a default configuration that is not at all secure. This blog helps in set up SSH service configuration securely.
Just remember to always restart the SSH service to update the configuration after performing changes by using the below command:
service sshd restart
(1) root user should be disabled
root user denotes a user having superuser access on a system. If attackers somehow access your root account on the system, it leads to disastrous consequences. Hence, It is advisable to disable root login.
Check options using the below command:
less /etc/ssh/sshd_config
The below settings prohibit password authentication and allow only passwordless authentication.

If you want to totally disable root authentication, just use no in front of PermitRootLogin
PermitRootLogin no
(2) Implement a strong encryption algorithm while configuring a secure shell
Cryptography is key to the confidentiality and integrity of the system. Below is the list of secure algorithms recommended by NIST:
| Algorithm | Type of Algorithm | Specification | Key size | Usage |
| Elliptic Curve Diffie-Hellman (ECDH) Key Exchange | Asymmetric algorithm | NIST SP 800-56A | Curve P-384 | key establishment |
| Advanced Encryption Standard (AES) | Symmetric block cipher | FIPS PUB 197 | 256 bit keys | information protection |
| Elliptic Curve Digital Signature Algorithm (ECDSA) | Asymmetric algorithm | FIPS Pub 186-4 | Curve P-384 | digital signature |
| Secure Hash Algorithm (SHA) | Hashing technique | FIPS Pub 180-4 | SHA-384 | convert any input into fixed size data |
| Diffie-Hellman (DH) Key Exchange | Asymmetric algorithm | IETF RFC 3526 | 3072-bit modulus | key establishment |
| RSA | Asymmetric algorithm | FIPS PUB 186-4 | 3072 bit-modulus | key establishment |
| RSA | Asymmetric algorithm | NIST SP 800-56B rev 1 | 3072-bit modulus | digital signatures |
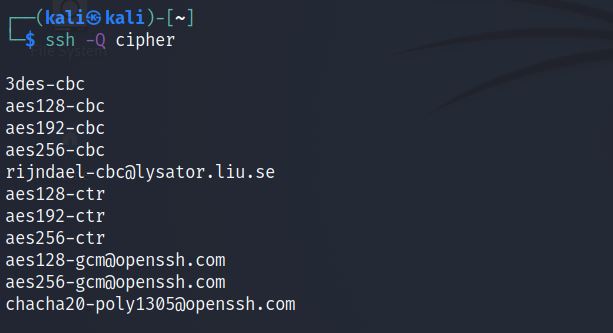
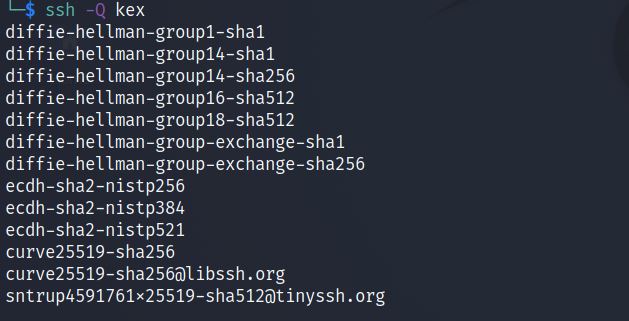
Check which algorithms are supported by the system by using the below commands:
ssh -Q cipher
ssh -Q kex
ssh -Q key

ssh -Q mac

(3) Configure passwordless logins
While authenticating SSH using username and password, both credentials are communicating via an encrypted channel. However, an attacker may try brute force against SSH username and password. If you are using the same desktop for SSH, you can configure passwordless login to access remote desktops/systems.
less /etc/ssh/sshd_config
(4) Logging should be enabled in detailed mode
SSH server runs, IT system will produce the logging messages in sshd.log. Ensure enabling logging in detailed mode.
(5) Always configure banners for warning
It is recommended to create a banner for users who are trying to access the system using SSH.
(6) Configure automatic logout
Look sshd_config file, and change the below options:
ClientAliveInterval 0 ClientAliveCountMax 3
ClientAliveInterval determines the time to keep the connection alive. ClientAliveCountMax is the limit of staying unresponsive before being disconnected. This will configure automatic logout if the user login remotely using SSH protocol.
ClientAliveInterval 300 ClientAliveCountMax 2
(7) Change the default SSH port
SSH default port is 22. You can check by just looking by below command:
less /etc/ssh/sshd_config
It is recommended to change it to a different port number. This particular step just increases the little time of the attacker to identify an open SSH port.
Port 2123
(8) Disable X11 forwarding
X11forwarding allows remote users to access GUI-based applications like browsers if the configuration is similar to the below command in sshd_config:
X11Forwarding yes
If you want to disallow it, just change the option to no
X11Forwarding no
(9) Check SSH Protocol 1 is disabled
Protocol 1 is the original version of SSH and is now considered as insecure. Protocol 1 is currently used for legacy systems. You can check the configuration by looking into the file /etc/ssh/sshd_config file. If Protocol 1 or Protocol 1, 2 is available, then it may be vulnerable to different CVEs which is the application for SSH Protocol 1.
less /etc/ssh/sshd_config
Just change and allow only Protocol 2
Protocol 2
(10) Username/Password login should be disabled
Password-based authentication is an insecure way of authentication. You can check the same just by auditing the sshd_config file. If you found the below option, that simply means the system is allowing password-based authentication.
PasswordAuthentication yes
Just change it to no to disable it.
PasswordAuthentication no
Conclusion
This blog gives a brief overview of the configuration of SSH hardening steps to secure it from bad people. As told in beginning, always restart the SSH service to update configurations.
Subscribe us to receive more such articles updates in your email.
If you have any questions, feel free to ask in the comments section below. Nothing gives me greater joy than helping my readers!
Disclaimer: This tutorial is for educational purpose only. Individual is solely responsible for any illegal act.








